ISO 27001 A.8.15 Logging Checklist
A.8.15 Logging is a crucial control within the ISO/IEC 27001:2022 standard. It focuses on the generation, protection, and analysis of logs to ensure security, compliance, and operational effectiveness. Logging is a fundamental aspect of information security management as it helps in detecting and responding to security incidents, ensuring accountability, and meeting regulatory requirements. This control involves several key aspects, each addressing specific requirements and challenges that an organisation must manage effectively.
Scope of Annex A.8.15
Logging involves the systematic recording of events that occur within an organisation’s information systems. This includes capturing details about user activities, system changes, access to sensitive information, and security incidents. Effective logging is essential for several reasons:
- Security Monitoring: Logs provide a trail of activities that can be monitored to detect unauthorised access or other malicious activities.
- Incident Response: In the event of a security incident, logs are invaluable for investigating the incident, understanding its scope, and taking corrective actions.
- Compliance: Many regulations and standards require organisations to maintain logs as evidence of their security practices and compliance efforts.
- Accountability: Logs help ensure that actions taken by users and administrators are tracked, promoting accountability and transparency.
Implementing A.8.15 Logging requires a comprehensive approach that addresses the generation, protection, analysis, and retention of logs. Below, we outline the key aspects and challenges of each step, along with solutions and associated ISO 27001:2022 clauses and requirements.

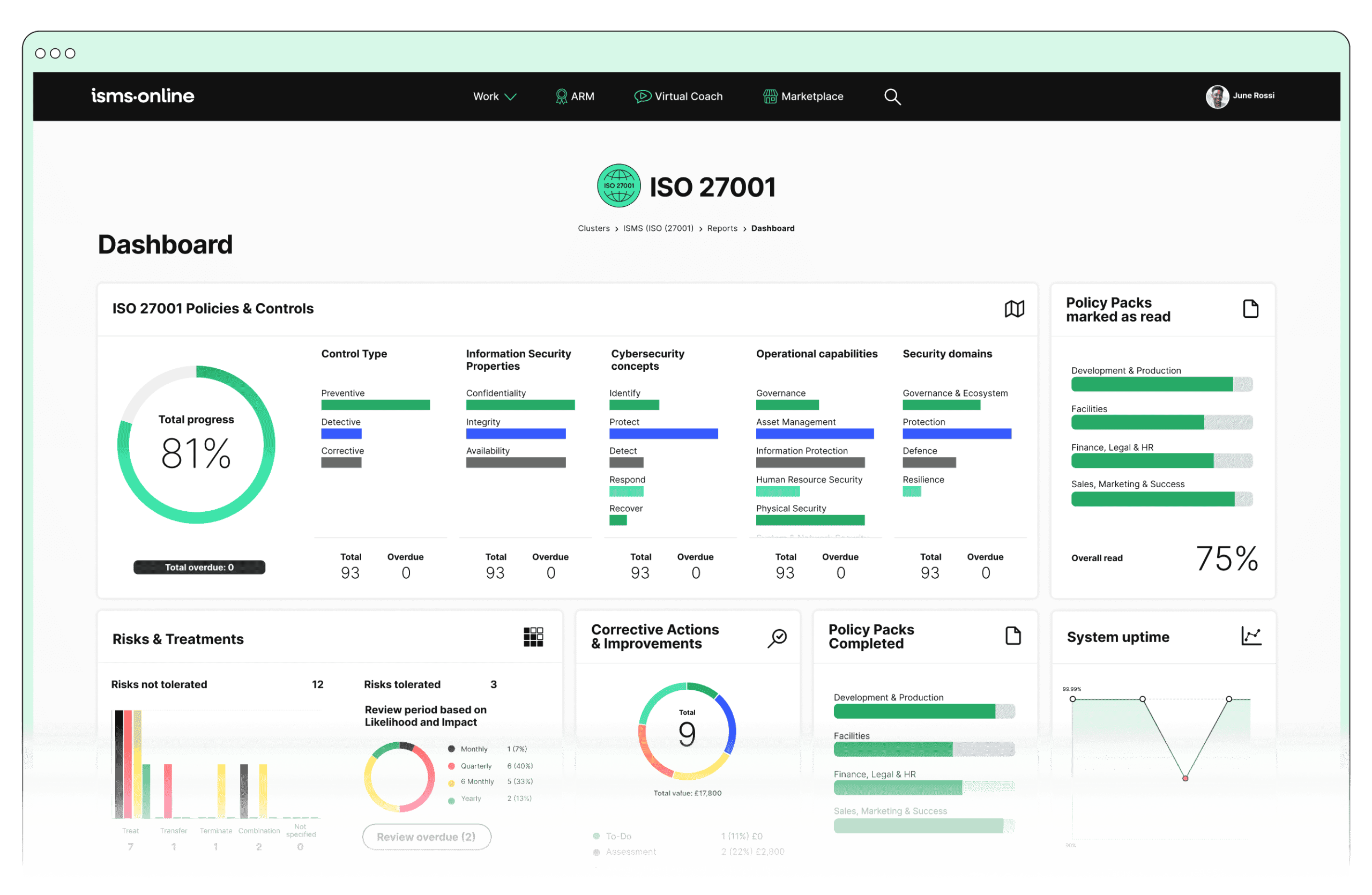
ISO 27001 made easy
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.8.15? Key Aspects and Common Challenges
Log Generation
- Purpose: Logs must be generated for all significant events, including security incidents, user activities, system changes, and access to sensitive information.
- Challenges: Ensuring comprehensive coverage and consistency in log generation across various systems and applications can be challenging. Different systems may have different logging capabilities and formats, making standardisation difficult.
- Solutions: Implement a centralised logging solution, such as a SIEM (Security Information and Event Management) system, that aggregates logs from different systems. Use standardised logging formats like JSON or XML.
- Details to Capture: Logs should include details such as the date and time of the event, user identification, type of event, and success or failure of the event.
- Challenges: Capturing detailed and accurate information without overwhelming storage and processing capabilities can be problematic. There is a need to balance between detail and performance impact.
- Solutions: Define and enforce logging policies specifying required details. Implement log rotation and archiving to manage storage effectively.
Log Protection
- Integrity: Logs must be protected against unauthorised access, modification, and deletion to ensure their integrity. This involves implementing access controls, encryption, and secure storage mechanisms.
- Challenges: Protecting log integrity involves sophisticated security measures and constant monitoring to prevent tampering or unauthorised access. This requires robust access control policies and technical implementations.
- Solutions: Use access control lists (ACLs) and encryption to protect log files. Regularly review access permissions and implement tamper-evident logging mechanisms.
- Availability: Logs should be available for analysis when needed, implying that they should be backed up regularly and stored in a secure location.
- Challenges: Ensuring availability while maintaining security is a delicate balance. Secure storage solutions must also allow for timely retrieval and analysis, which can be resource-intensive.
- Solutions: Implement redundant storage solutions and regular backups. Use cloud storage solutions with high availability for log storage.
Log Analysis
- Regular Monitoring: Logs should be monitored regularly to detect unusual or suspicious activities that might indicate a security breach or policy violation.
- Challenges: Regular monitoring requires significant resources and advanced tools to identify and prioritise alerts effectively. The volume of logs can be overwhelming without automated tools.
- Solutions: Use Security Information and Event Management (SIEM) systems to automate log monitoring and alerting. Employ machine learning algorithms to identify anomalies.
- Automated Tools: Employing automated tools for log analysis can help in quickly identifying patterns, anomalies, and potential security incidents.
- Challenges: Implementing and maintaining automated analysis tools involves technical expertise and continuous tuning to reduce false positives and negatives.
- Solutions: Regularly update and tune automated tools based on new threats and patterns. Use threat intelligence feeds to enhance the effectiveness of automated analysis.
- Incident Response: Logs play a vital role in incident response by providing evidence and supporting investigations into security incidents.
- Challenges: Integrating logs into incident response workflows requires seamless coordination between logging systems and incident response teams, which can be complex to achieve.
- Solutions: Establish clear incident response procedures that include log analysis as a critical step. Ensure incident response teams are trained in using log data for investigations.
Compliance and Reporting
- Regulatory Requirements: Organisations must ensure that their logging practices comply with relevant regulatory requirements and standards.
- Challenges: Keeping up with changing regulatory requirements and ensuring that logging practices meet these standards can be demanding. Compliance audits require meticulous documentation and proof.
- Solutions: Regularly review and update logging practices to ensure compliance with regulations. Use compliance management tools to track and document compliance efforts.
- Audit Trail: Maintaining a detailed audit trail through logs helps in demonstrating compliance during audits and reviews.
- Challenges: Creating and maintaining a comprehensive audit trail that meets compliance standards involves consistent logging practices and rigorous documentation.
- Solutions: Implement detailed logging policies and ensure all logs are stored in a tamper-evident manner. Use automated tools to generate compliance reports.
Retention Policies
- Retention Period: Logs should be retained for a period consistent with organisational policies, legal requirements, and industry best practices.
- Challenges: Determining appropriate retention periods and ensuring compliance with varying legal requirements can be complex. Managing storage for long-term retention also poses a challenge.
- Solutions: Define retention policies based on legal and business requirements. Use archival solutions that support long-term storage and retrieval.
- Disposal: At the end of the retention period, logs should be disposed of securely to prevent unauthorised access to sensitive information.
- Challenges: Securely disposing of logs without compromising sensitive information requires strict procedures and reliable execution, which can be operationally challenging.
- Solutions: Implement secure disposal methods such as shredding or secure deletion software. Ensure that disposal procedures are well-documented and regularly reviewed.
By implementing robust logging mechanisms, organisations can enhance their ability to detect, respond to, and investigate security incidents, thereby strengthening their overall information security posture.

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.8.15
ISMS.online provides several features that are instrumental in demonstrating compliance with A.8.15 Logging:
- Incident Management:
- Incident Tracker: Allows for detailed logging of incidents, capturing essential information such as date, time, user, and nature of the incident.
- Workflow and Notifications: Ensures that all incidents are tracked and managed efficiently with automated workflows and notifications.
- Audit Management:
- Audit Templates: Facilitates the documentation of audit logs, ensuring all events are recorded in compliance with A.8.15.
- Corrective Actions: Provides a mechanism to log and track corrective actions stemming from audit findings, maintaining a detailed audit trail.
- Policy Management:
- Policy Templates and Pack: Enables the creation and communication of logging policies, ensuring that all stakeholders are aware of their logging responsibilities.
- Version Control: Maintains historical versions of logging policies, demonstrating compliance with documentation requirements.
- Risk Management:
- Risk Monitoring: Includes dynamic risk maps and risk monitoring features that log and track risk assessments and treatments.
- Risk Bank: Stores information on risks and related logs, supporting compliance with regular monitoring and review requirements.
- Compliance Management:
- Regs Database and Alert System: Helps in ensuring that logging practices are aligned with regulatory requirements by providing access to a database of regulations and an alert system for updates.
- Reporting: Facilitates comprehensive reporting on compliance status, including logging activities and retention practices.
- Business Continuity:
- Continuity Plans: Logs details of business continuity plans, including testing and activation logs, ensuring readiness for disruptions.
- Test Schedules and Reporting: Tracks and logs tests of business continuity plans, providing evidence of preparedness.
- Documentation Management:
- Doc Templates and Version Control: Ensures that all log-related documentation is controlled, updated, and accessible as needed.
- Collaboration Tools: Facilitates collaborative creation and review of logging documentation.
By leveraging these features, organisations can effectively demonstrate compliance with A.8.15 Logging, ensuring that logs are generated, protected, analysed, and retained in accordance with ISO 27001:2022 requirements.
Detailed Annex A.8.15 Compliance Checklist
Log Generation
Log Protection
Log Analysis
Compliance and Reporting
Retention Policies
By following this detailed compliance checklist, organisations can systematically address the requirements of A.8.15 Logging, overcoming common challenges and demonstrating robust compliance with ISO 27001:2022 standards.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.8.15
Ready to take your information security management to the next level?
Contact ISMS.online today and book a demo to see how our comprehensive suite of tools can help you achieve compliance with A.8.15 Logging and other ISO 27001:2022 controls.
Our platform is designed to simplify your compliance journey, offering intuitive features that streamline policy management, incident tracking, audit documentation, and more.
Don’t wait to enhance your security posture and ensure compliance.